Okay, so I'll try to get cert-chain of public CA onto the switch (EST connection) and after that enroll PKI-certificates (RadSec connection). It may take few days but I'll surely give a feedback.
-------------------------------------------
Original Message:
Sent: May 06, 2026 11:07 AM
From: DB86
Subject: ClearPass 6.12.7 problem with EST roll-out
Yea i get thats a lab guide, but the issuer of the cert would be your public CA your correct.
Yea that shouldnt be a problem. As long as the device your using with EST trusts the issuer of the certificates, through configuration or out of the box, it should be fine.
I would also not use wildcard certificates as they are not secure, and becoming more and more unsupported.
------------------------------
Dustin Burns
Lead Mobility Engineer @Worldcom Exchange, Inc.
ACCX 1271| ACMX 509| ACSP | ACDA | MVP Guru 2022-2023
If my post was useful accept solution and/or give kudos
Original Message:
Sent: May 06, 2026 10:29 AM
From: Greg83
Subject: ClearPass 6.12.7 problem with EST roll-out
Hello Dustin,
Thank you for quick reply and the how-to document (the pictures are very low resolution, I can't read it). At first sight I saw that you use HTTPS certificates issued from Onboard PKI which is a root. This will work in lab but in a production presenting a landing page for self-register or register with a unknown certificate issuer will pop up warnings on guest devices - that's why I've implemented public certificate which is trusted from almost every OS cert-store. You can bet the certificate provider dont let me doing a sub-ca behalf their name ;-)
So the question is can I use separate certificates for HTTPS and EST? Maybe with other FQDN's, ports on EST-settings on the switch, whatsoever?
Best Regards,
Greg
Original Message:
Sent: May 06, 2026 10:11 AM
From: DB86
Subject: ClearPass 6.12.7 problem with EST roll-out
Did you add the root cert to the switch in its trust? If not, then try that next. If its there, then the cert chaining may be off. See attached a guide we wrote up quick for an EST enrollment via ClearPass for RADSEC.
------------------------------
Dustin Burns
Lead Mobility Engineer @Worldcom Exchange, Inc.
ACCX 1271| ACMX 509| ACSP | ACDA | MVP Guru 2022-2023
If my post was useful accept solution and/or give kudos
Original Message:
Sent: May 06, 2026 03:53 AM
From: Greg83
Subject: ClearPass 6.12.7 problem with EST roll-out
Hello community,
I've implemented a ClearPass instance preparing it firstly to provide a landing page for guest registration. Following best practices I've added to all nodes
a public wildcard certificate for RSA HTTPS. Doing this I've also added certificate provider cert-chain to CPPM Trust List.
Now I'm trying to implement EST certficate enrollment for Aruba switches to be able to connect NAD's through RadSec without carrying about certificate expiration.
I've added Onboard as a sub-ca signed by our PKI-Root (different, private domain opposite to public cert. containing our public domain).
Then I've add a TA-profile on a AOS-S switch (2930M running WC.16.11.0027) executing following commands:
crypto pki ta-profile https-ca-chain
copy tftp ta-certificate https-ca-chain <TFTP-Server> onboard-chain.pem
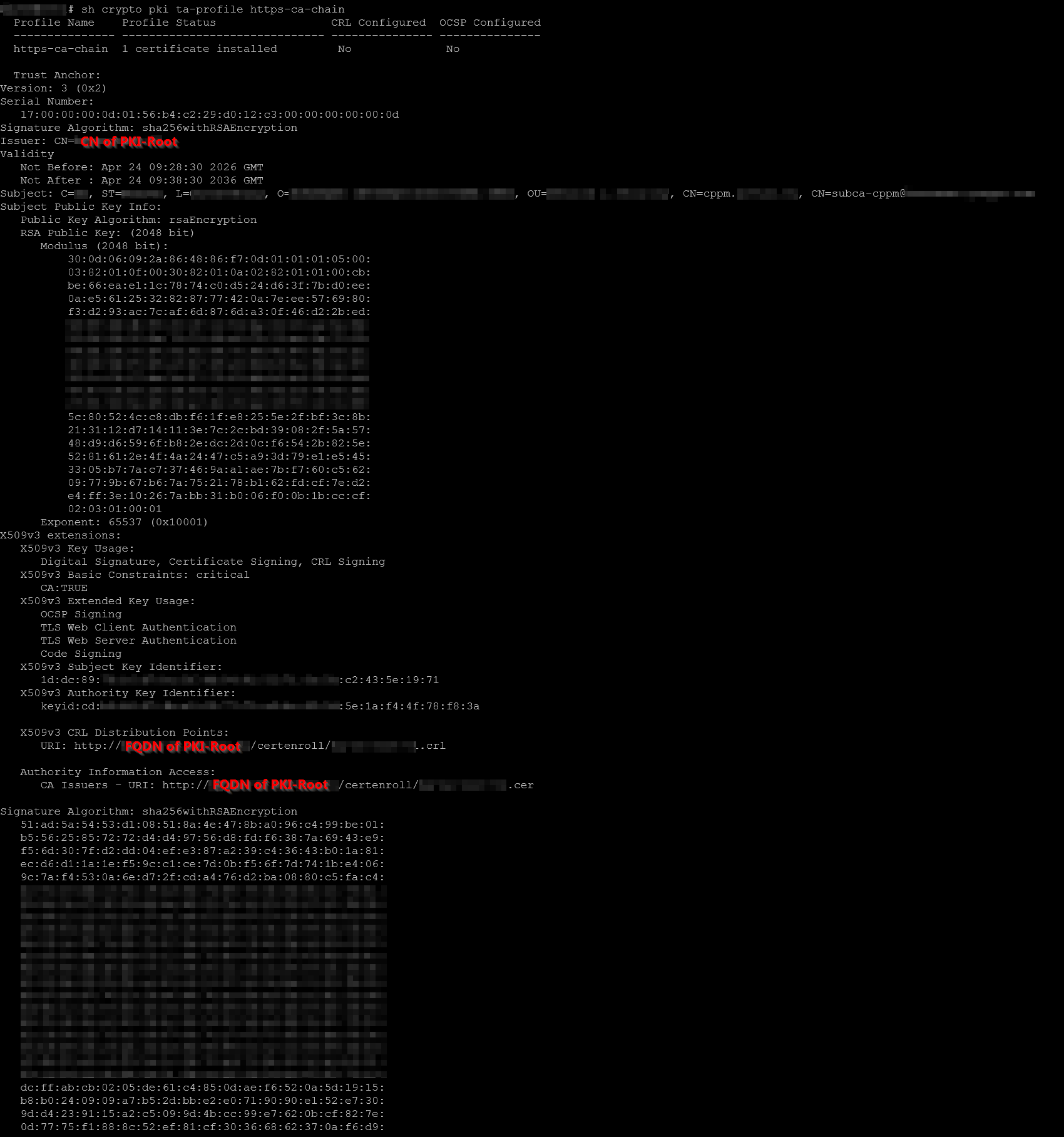
sh crypto pki ta-profile https-ca-chain:
showing issuing through PKI-Root, Subject: CN=cppm.<internal-domain>, CN=subca-cppm@<mail-domain>
est-server "est-onboard" "Onboard->Certificate Authorities->Sub-CA cert->Edit->EST URL" (https://<hostname>/.well-known/est/ca:3 hostname from EST-URL and CN in certificate are different - maybe it's the cause?)
est-server est-onboard user-name <Onboard-user> secret <Onboard-user password>
crypto pki enroll-est-certificate "est-onboard" certificate-name "est-cert" ta-profile "https-ca-chain" subject common-name <Switch CN> org <ORG> locality <CITY> state <STATE> country <COUNTRY> usage radsec-client
crypto pki enroll-est-certificate est-onboard certificate-name est-cert ta-profile est-onboard usage radsec-client
After that I can see that executing "sh est est-onboard status" command shows "SSL connect error".
Digging with "debug security crypto" I was able to see this message:
CRYP mestClientTask:Unable to find root certificate to validate certificate against.
Any ideas what could cause this issue? AFAIK the TA-profile contains required root information?
Here's the output from "sh crypto pki ta-profile https-ca-chain" (obfuscated):
Best Regards,
Greg
-------------------------------------------