Hi,
I'm currently working on a configuration, that tunnels Guest Clients to a central DMZ VLAN. I planned to use Tunnel Groups, however it seems the feature is not really working in L2.
Please correct me if I got anything wrong:
We have 4 MDs in our network - 2 Site MDs (Remote 1 and Remote2) and 2 Central MDs (DMZ1 and DMZ2).
For redundancy reasons, we want to use tunnel groups to force the traffic through the primary tunnel.
Tunnel Groups are only configured at the Remote site, as they can't be applied at the Central configuration.
I noticed the following problem with the concept: At the Central site, each DMZ MD has two active Tunnels to the Remote MDs and an uplink connection to the wired network. I can't figure out any configuration that would not end in a loop.
The green arrows should display unidirectional traffic flow. The primary tunnels are full duplex, the secondary tunnels are blocked, however able to receive traffic.
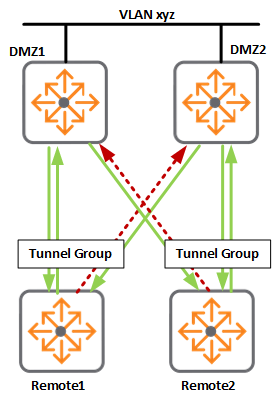
- Client at Remote1 sends an ARP
- DMZ1 receives the ARP and forwards it via L2 Tunnel to Remote 2 and via wired Ports to DMZ2
- Remote 2 receives the ARP via it's secondary tunnel group member tunnel and forwards it back to DMZ2 via the primary tunnel - In the meantime, DMZ2 receives the ARP on it's wired Ports and sends it out through both downstream GRE Tunnels.
- Back to step 1
The command "no inter-tunnel-flooding" prevents the flooding between two GRE tunnels, however it is not fixing the problem.
As both DMZ1 and DMZ2 are linked via wired ports, DMZ2 would receive the ARP on the wired interface and "no inter tunnel flooding" would not work.
Is there any way to have a redundant L2 Uplink to the Central MDs?