-------------------------------------------
Original Message:
Sent: Mar 27, 2026 04:38 PM
From: Collin.Koss
Subject: Retrieving wpa-passphrase - New Central API
In the meantime, I did find another way for you to validate manually if you have some devices to test with. After updating the SSID, you can remote into one of the APs where the profile is applied and run the command: show run no-encrypt . This will reveal the passphrase in the remote session. Still following up on the hide/unhide functionality in Central vs Classic. Hope this tides you over until then!
Cheers,
Collin
Original Message:
Sent: Mar 27, 2026 01:53 PM
From: cauliflower
Subject: Retrieving wpa-passphrase - New Central API
Thanks Collin,
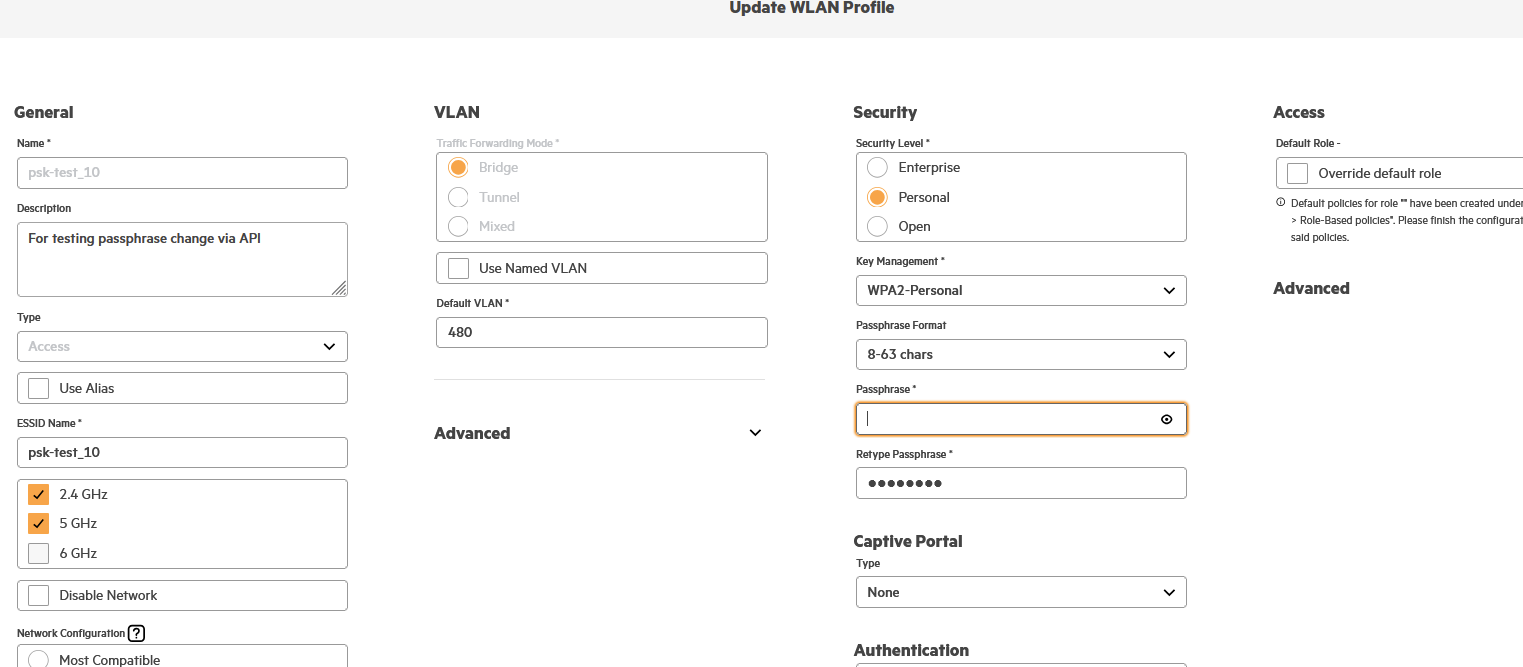
I tried that doing that, when I hover over the password field (contaning the black dots) the eye doesn't appear, if I click into the field then my cursor appears in the field as you'd expect, and the black dots disappear, At that point the eye does appear, however if I click on the eye at that point all that happens is the black dots reappear! I tried with Chrome and Firefox with the same result. I'm trying this on this page:
Am I doing something wrong? Note this is New Central.
Guy
Original Message:
Sent: Mar 27, 2026 12:52 PM
From: Collin.Koss
Subject: Retrieving wpa-passphrase - New Central API
Hello!
You're correct that there is no way to validate the password directly via API. It will always be returned encrypted as you have observed. You CAN however validate the password of an SSID in the UI if you just want to make sure the API is working. You can do this editing an SSID with the pencil icon and navigating to the security screen. There should be a crossed out eye symbol next to the passphrase field. If you are not able to see this let me know with details and I can try to help from there!
Original Message:
Sent: Mar 23, 2026 11:24 AM
From: cauliflower
Subject: Retrieving wpa-passphrase - New Central API
Hello,
We have a requirement to be able to change a wpa-passphrase for a bridged SSID via the API. At the moment we are not live with AOS10/New Central so we are just testing right now.
I have found the API calls to change the password, and that returns 'success', but I can't find a way to verify that the change has taken place. Using the API I get an encrypted vault:v2 string when I do a 'get' on the SSID details. And even on the GUI I can't see a way to view the password manually to make sure the change is taking place.
What is the best way to be sure that the passphrase change has been successful?
Thank you,
Guy
-------------------------------------------