Hi all,
How do I setup Role Mapping to use Profiling information from the Endpoint Repository?
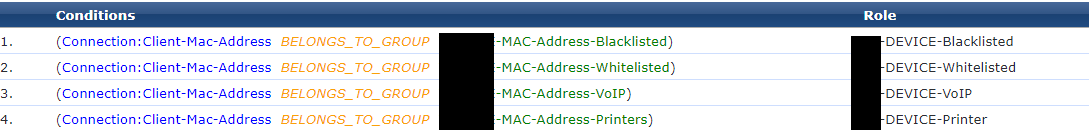
I've setup MAC Authentication Bypass for devices that do not support 802.1x, using a Static Host List and the following role mapping:
Too ensure a MAC adres can't just simply be spoofed, I want to use the endpoint profiling information to verify the device when Role mapping. I would like to use the 'Device Category' and maybe even the 'Device OS Family' as well:
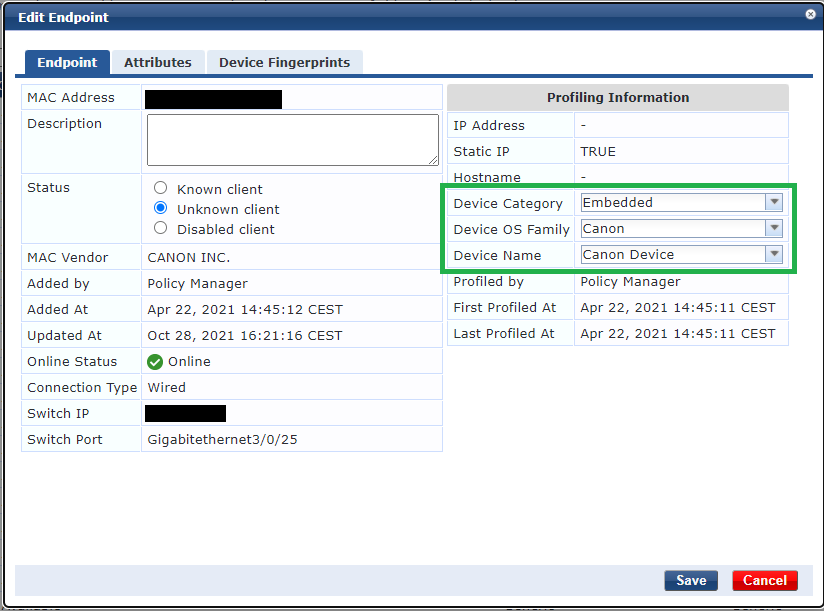
I've red about adding Attributes to every known endpoint and using the attributes in role mapping, but i want this process to be as automatic as it can be; without adding attributes manually to every (e.g.) printer. I can't seem to find the proper role mapping rules for this.
How do I setup my role mapping to use the information gained via profiling?
------------------------------
Lex
------------------------------