What is the type of switch? ArubaOS switches and AOS-CX switches with concurrent onboarding enabled on the port do 802.1X and MAC authentication in parallel. It is normal that you see both types of authentication and as long as the 802.1X is successful, the outcome of the MAC authentication is ignored by the switch.
What is not normal, is the MAC authentication repeating every 30 seconds. I see an ACCEPT in Access Tracker, but you mention a fail, which is in conflict. For MAC authentication you should probably never return a REJECT, but always a SUCCESS, and then use ACLs/Roles/VLAN to make sure that unknown client can be profiled, but don't have a lot of network access. You can use the [Allow All MAC Auth] Authentication method for that, and during the enforcement decide what enforcement to return.
If this above does not help, I would recommend reaching out to your Aruba partner or Aruba Support to have a look together and understand what is happening.
------------------------------
Herman Robers
------------------------
If you have urgent issues, always contact your Aruba partner, distributor, or Aruba TAC Support. Check
https://www.arubanetworks.com/support-services/contact-support/ for how to contact Aruba TAC. Any opinions expressed here are solely my own and not necessarily that of Hewlett Packard Enterprise or Aruba Networks.
In case your problem is solved, please invest the time to post a follow-up with the information on how you solved it. Others can benefit from that.
------------------------------
Original Message:
Sent: Aug 30, 2021 06:35 AM
From: Lex Krijnen
Subject: Same client is re-authenticating after succesfull 802.1x Authentication
I've setup two authentication methods (services) for wired: EAP-TLS (User certs) and EAP-MD5 (MAB based on a static-host-list).
Once the connected client is successfully authenticated using EAP-TLS, it still tries to re-authenticate using the MAC-address. See screenshot and timestamps for details (marked with orange is the same client). This triggers an authentication failure, because the MAC-address is not known by ClearPass, resulting in a wrong VLAN assignment for the connecting client.
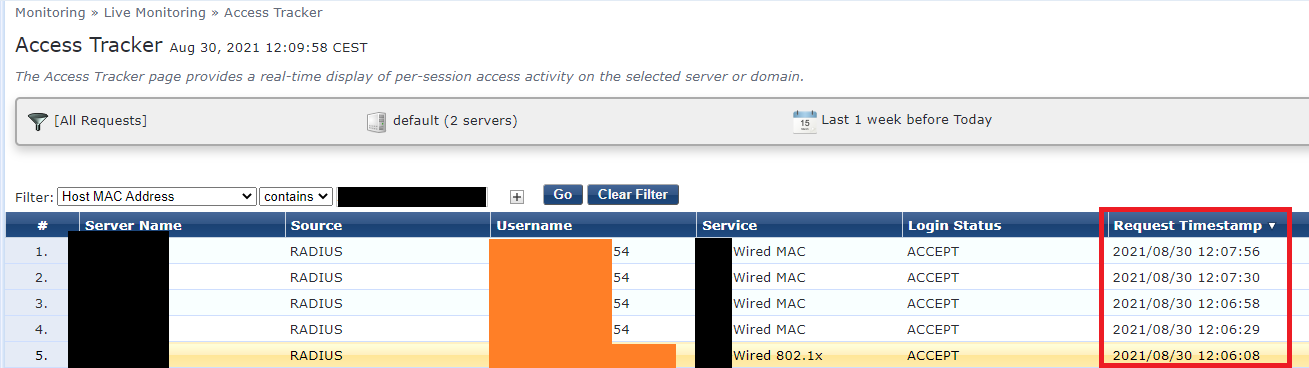
Why is this happening? I've set the Enforcement Profile 'Radius:IETF:Session-Timeout' attribute to 10800 seconds, and the client successfully authenticates the first time (using the installed user-certificate).
Thanks in advance!
------------------------------
Lex
------------------------------