Hey man thanks for your insight, I appreciate it.
Original Message:
Sent: Jul 11, 2025 10:55 AM
From: willembargeman
Subject: Setting endpoint attribute as role dynamically
Yes correct. It is not required to create the tags / roles but then you can't built the dynamic policies.
If you just want to have the username / IP mapping available there is no need to create TAGs and Roles.
------------------------------
Willem Bargeman
Systems Engineer Aruba
ACEX #125
Original Message:
Sent: Jul 11, 2025 10:31 AM
From: MT9
Subject: Setting endpoint attribute as role dynamically
Okay I think I got it. So the Palo will see the roles/user-ids come in, but there still needs to be a TAG created that matches the user-ID name in order to build the policy. You cannot just reference a user-id name without having the tag created first. I think that's okay in that there's only 20 or so categories and sub categories. Any models that are part of the more device specific policies will need to be defined. I don't think it makes a ton of sense to preload the tags into the firewalls. That's getting more outside my wheelhouse.
We have about 600 device specific medical device models.
Original Message:
Sent: Jul 11, 2025 10:21 AM
From: willembargeman
Subject: Setting endpoint attribute as role dynamically
The integration is not an static IP map but Tags and dynamic address groups.
Within Palo Alto you need to define the Tag and an Address Group. The Address Group will match on one or more tags.
ClearPass will send the User-IP info the Palo Alto together with the Roles. The Roles on Palo will become Tags. Because a tag is added to an Dynamic Address Group you can built dynamic firewall policies.
Bottom line, tags need to defined manually in Palo and must matched the roles in ClearPass.
This is the integration guide: https://support.hpe.com/hpesc/public/docDisplay?docId=a00101503en_us
------------------------------
Willem Bargeman
Systems Engineer Aruba
ACEX #125
Original Message:
Sent: Jul 11, 2025 10:11 AM
From: MT9
Subject: Setting endpoint attribute as role dynamically
Perhaps my understanding is incorrect for the Palo integration (I'm still waiting for access to the test FW), but I was under the impression that roles would be interpreted as dynamic User-IDs not static IP-Tags on the firewall.
Original Message:
Sent: Jul 11, 2025 10:07 AM
From: willembargeman
Subject: Setting endpoint attribute as role dynamically
You can use the role mapping for that. However, you need to do the matching manually. For example: If "device type" eq X set role Y.
The method use built doesn't require the manual mapping. An the other side, you also need to create the TAGs in Palo Alto.
------------------------------
Willem Bargeman
Systems Engineer Aruba
ACEX #125
Original Message:
Sent: Jul 11, 2025 10:01 AM
From: MT9
Subject: Setting endpoint attribute as role dynamically
Thanks Willem. I'm not looking to use the roles in enforcement. I need the roles because those roles will be sent to the Palo Alto firewall via the XML API (through the integration) to be set as User-IDs for use in the Palo policies. If there's a better way than customizing the endpoint source to achieve this, I'd love to know.
I appreciate the reply.
Original Message:
Sent: Jul 11, 2025 07:21 AM
From: willembargeman
Subject: Setting endpoint attribute as role dynamically
It's not needed to customize the Endpoint auth source. Each value that is available can be fetched and used in policies. The attribute can be used in Role Mappings, enforcement policies and profiles. The following variable can be used in a profile %{Endpoint:Mediagate Category}.
Your solution is also a valid one
------------------------------
Willem Bargeman
Systems Engineer Aruba
ACEX #125
Original Message:
Sent: Jul 10, 2025 02:49 PM
From: MT9
Subject: Setting endpoint attribute as role dynamically
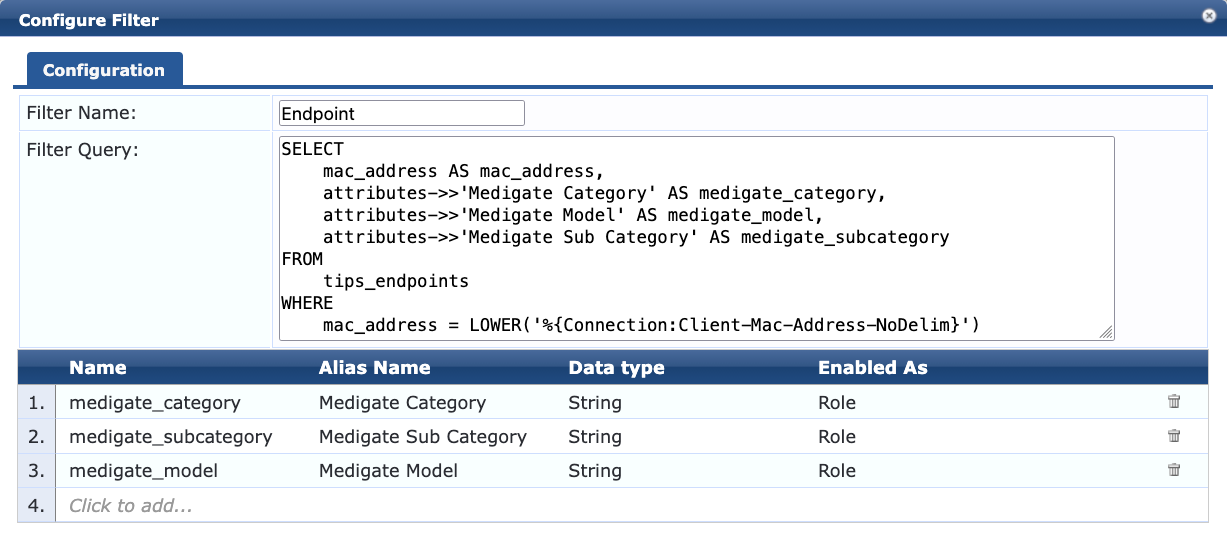
For future netizens, I was able to get it to work with this filter.
SELECT
mac_address AS mac_address,
attributes->>'Medigate Category' AS medigate_category,
attributes->>'Medigate Model' AS medigate_model,
attributes->>'Medigate Sub Category' AS medigate_subcategory
FROM
tips_endpoints
WHERE
mac_address = LOWER('%{Connection:Client-Mac-Address-NoDelim}')
Then I set role attributes and boom, they show up.
Original Message:
Sent: Jul 10, 2025 10:53 AM
From: MT9
Subject: Setting endpoint attribute as role dynamically
Hello,
I have an endpoint attributes that are fed by an API source. I want to use these attributes dynamically as roles. AKA, I want to set this attribute as a Role Attribute. These attributes are set in the endpoint. Do I need to set a custom filter query within the Endpoint Repository source to grab these attributes and then set them as a role attribute? Or is there a better way of doing this?
They are already specified as part of the dictionary attributes. As an example, here is what I have set in a particular endpoint.
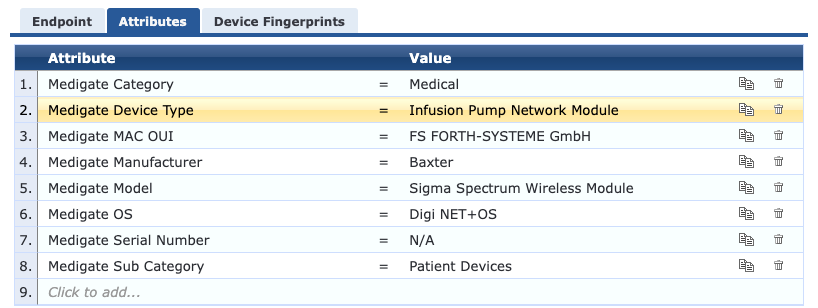
What I'm looking to do is to dynamically set roles. So Medigate Category, Medigate Sub Category and Medigate Model are all set dynamically as roles so I don't have to create every role manually as there will be always be new models that come into the system.
Any help would be appreciated.
Thanks.