Can you talk about why you want to do this? What is that first shared password designed to protect?
Are you trying to use the same SSID for devices that can't do dot1x and devices or users that can? Or, maybe a setup page for the .1X supplicant that you reach with the first password, and get ready for the Enterprise auth? AFAIK these would need separate SSIDs. As Shpat correctly noted, once you have one sort of L2 auth, there's not a way to do another sort, or to switch.
However, straight Enterprise auth is inherently more secure than shared password, as each user's connection is encrypted with different passwords, so I think shared-password + captive-portal would be less secure, as the second portal passwords would not add unique encryption. Anyone with the shared password could receive and decrypt all traffic over the air. Enterprise security prevents this.
------------------------------
Steve Bohrer
IT Infrastructure, Emerson College
------------------------------
Original Message:
Sent: May 23, 2025 05:45 AM
From: shivam
Subject: WPA2-Enterprise SSID Configuration: Pre-Authentication Password + RADIUS
Hello team,
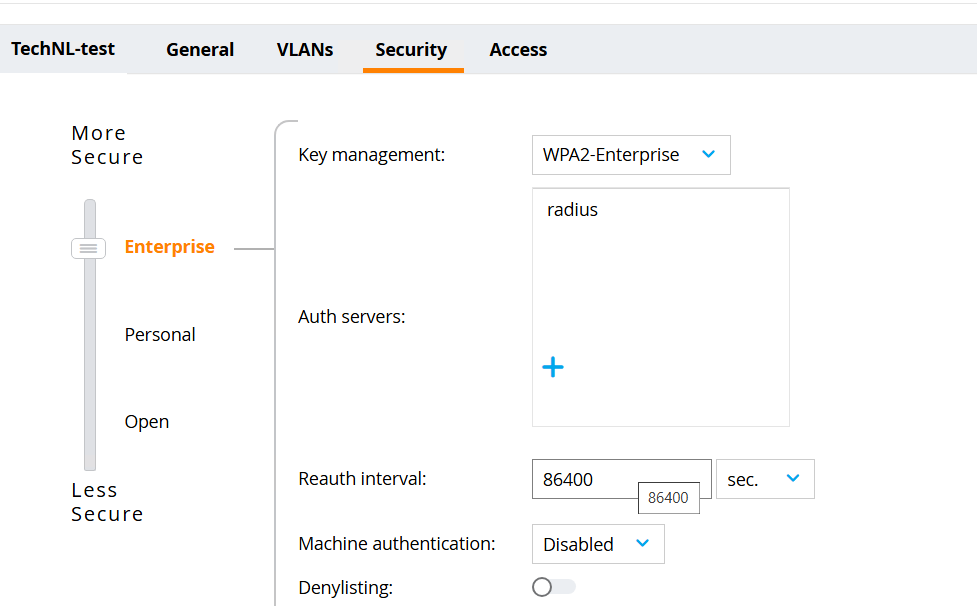
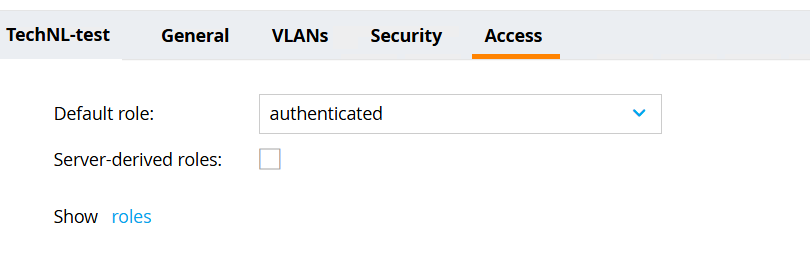
We have an MM/MD setup, there is an SSID configured with a WPA2-Enterprise SSID that uses CPPM as the authentication server.
We want to modify this SSID so that when a user tries to connect, they are first prompted to enter a password. After entering the correct password, the user should then proceed to RADIUS authentication.
please help me if it is possible.